Aggregate endpoint security risk scores with EDR, vulnerability data & Google Sheets
👤 Who it’s forSecurity teams, SOC analysts, and small-to-mid IT teams looking to automatically assess endpoint risk by combining known vulnerabilities with...
Get This WorkflowAbout This Workflow
Aggregate endpoint security risk scores with EDR, vulnerability data & Google Sheets
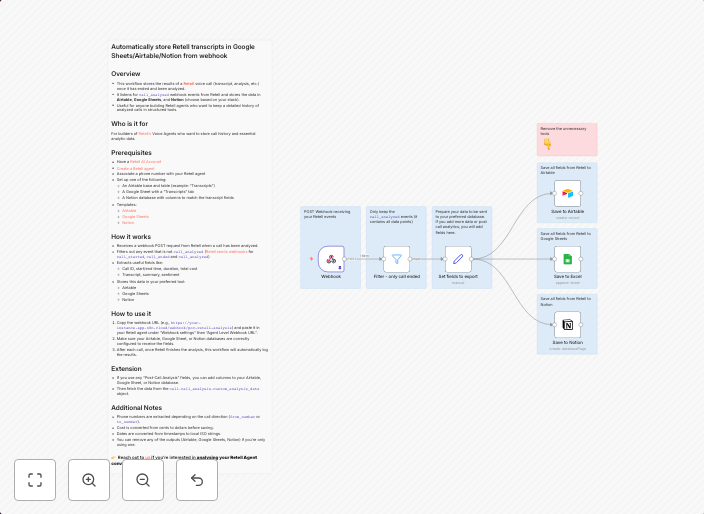
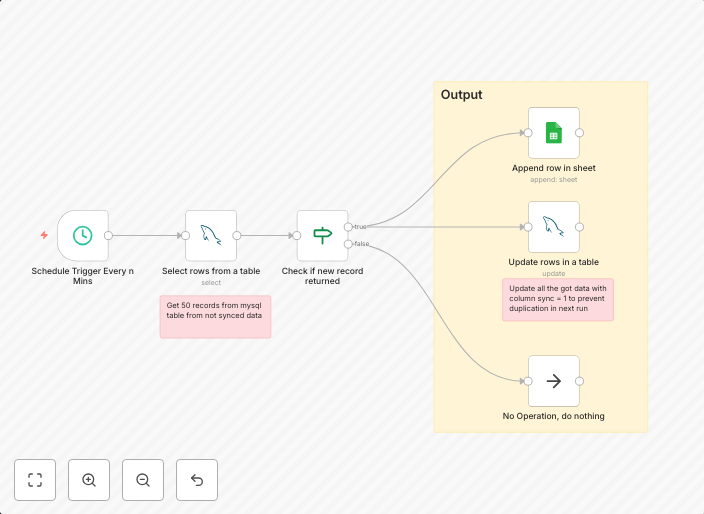
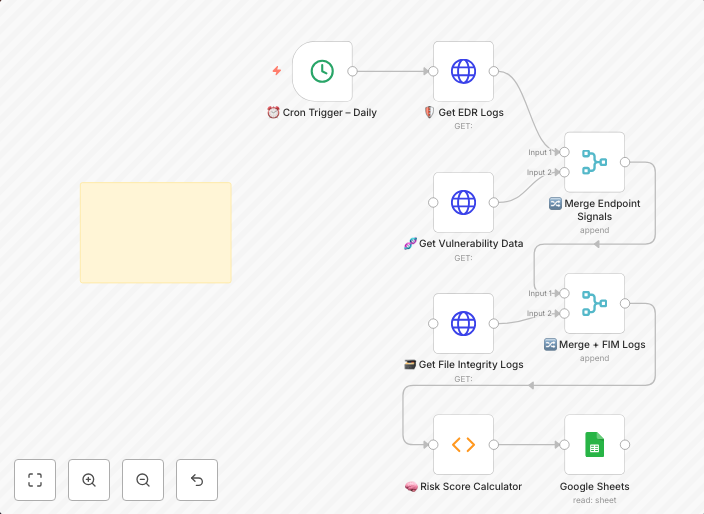
This workflow combines data from Endpoint Detection and Response (EDR) tools, vulnerability scanners, and Google Sheets to automatically calculate endpoint security risk scores. It aggregates this information to provide a comprehensive view of endpoint security posture, allowing for proactive risk management and incident response. The resulting risk scores can be used to prioritize remediation efforts and ensure compliance with security policies.
This workflow is designed for security teams, SOC analysts, and small-to-mid IT teams responsible for endpoint security, risk management, and compliance. It is ideal for organizations looking to streamline their security operations and improve their overall security posture.
- EDR integration: Connects to popular EDR tools to collect endpoint security event data and risk metrics.
- Vulnerability data aggregation: Collects and consolidates vulnerability data from various sources, including vulnerability scanners and databases.
- Google Sheets integration: Pushes calculated risk scores to a Google Sheets spreadsheet for real-time monitoring and analysis.
- Customizable risk scoring: Allows users to adjust the risk scoring formula to suit their organization's specific needs and security policies.
To start using this workflow, import it into your n8n account and configure the EDR, vulnerability data, and Google Sheets integrations according to your organization's endpoint security tools and Google Sheets setup. Customize the risk scoring formula to fit your specific security requirements and begin leveraging the workflow's automation capabilities to enhance your endpoint security posture.
Use This Workflow in n8n →Similar Workflows
Affiliate Disclosure: We may earn a commission if you sign up for n8n through our links. This doesn't affect our recommendations.