Automated GitHub scanner for exposed AWS IAM keys
Automated GitHub Scanner for Exposed AWS IAM Keys Overview This n8n workflow automatically scans GitHub for exposed AWS IAM access keys associated with your...
Get This WorkflowAbout This Workflow
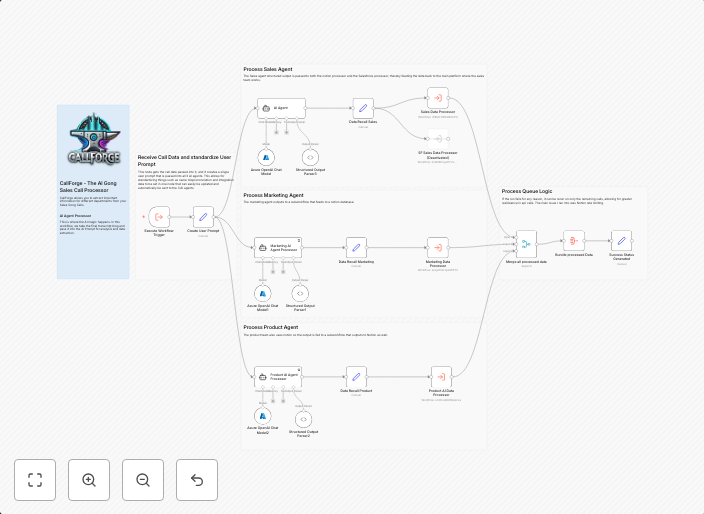
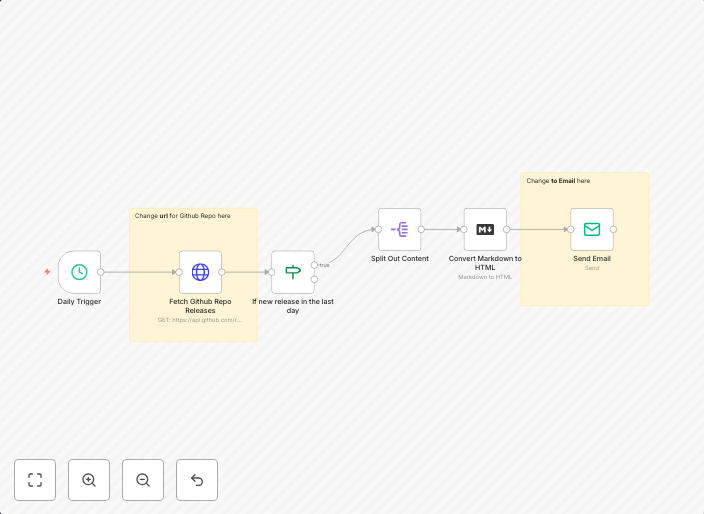
What This Workflow Does
This n8n workflow automatically scans GitHub repositories for exposed AWS IAM access keys, helping to identify potential security risks and prevent unauthorized access to your AWS resources. The workflow continuously monitors your GitHub repositories, detecting and reporting any exposed IAM keys it finds. By automating this process, you can ensure your AWS environment remains secure and compliant.
Who Should Use This
This workflow is ideal for security and compliance teams, DevOps engineers, and developers who want to maintain a secure AWS environment and prevent data breaches. It's also suitable for businesses that rely heavily on AWS services and need to ensure their access keys are not exposed.
Key Features
- Automated GitHub scanning: The workflow continuously scans your GitHub repositories for exposed AWS IAM access keys.
- Real-time detection: It detects exposed keys in real-time, providing immediate notifications and alerts.
- Customizable: You can customize the workflow to scan specific repositories, branches, or users, depending on your needs.
- Integration with AWS: The workflow integrates with AWS to provide detailed information about exposed IAM keys, making it easier to remediate security risks.
How to Get Started
To use this workflow, simply import it into your n8n instance, then customize the workflow settings to match your GitHub and AWS configurations. From there, the workflow will take care of continuously scanning your GitHub repositories for exposed IAM keys, providing you with real-time alerts and notifications.
Use This Workflow in n8n →Similar Workflows
Affiliate Disclosure: We may earn a commission if you sign up for n8n through our links. This doesn't affect our recommendations.