Monitor SSL certificates for brand-impersonating domains with crt.sh, Urlscan.io and Slack
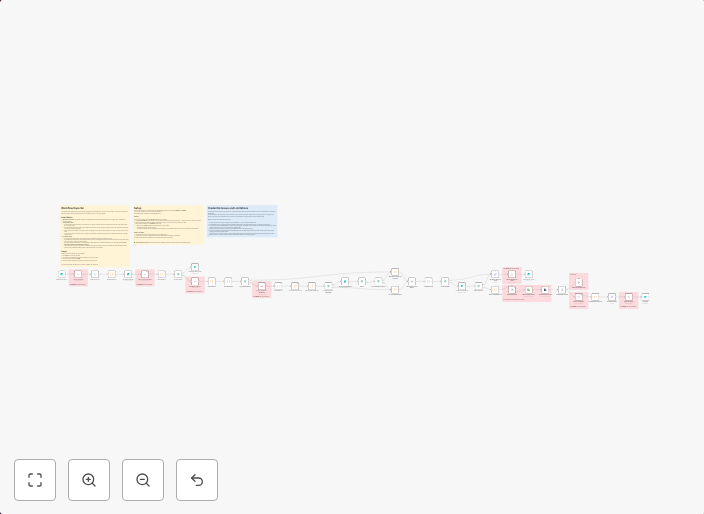
Phishing Lookout (Typosquatting) and Brand Domain MonitorThis workflow monitors SSL certificate logs to find and scan new domains that might be...
Get This WorkflowAbout This Workflow
Monitor SSL certificates for brand-impersonating domains with crt.sh, Urlscan.io and Slack
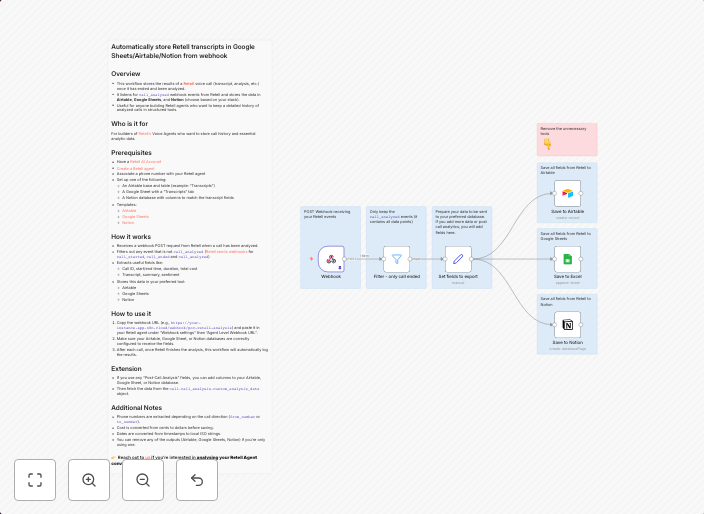
What This Workflow Does
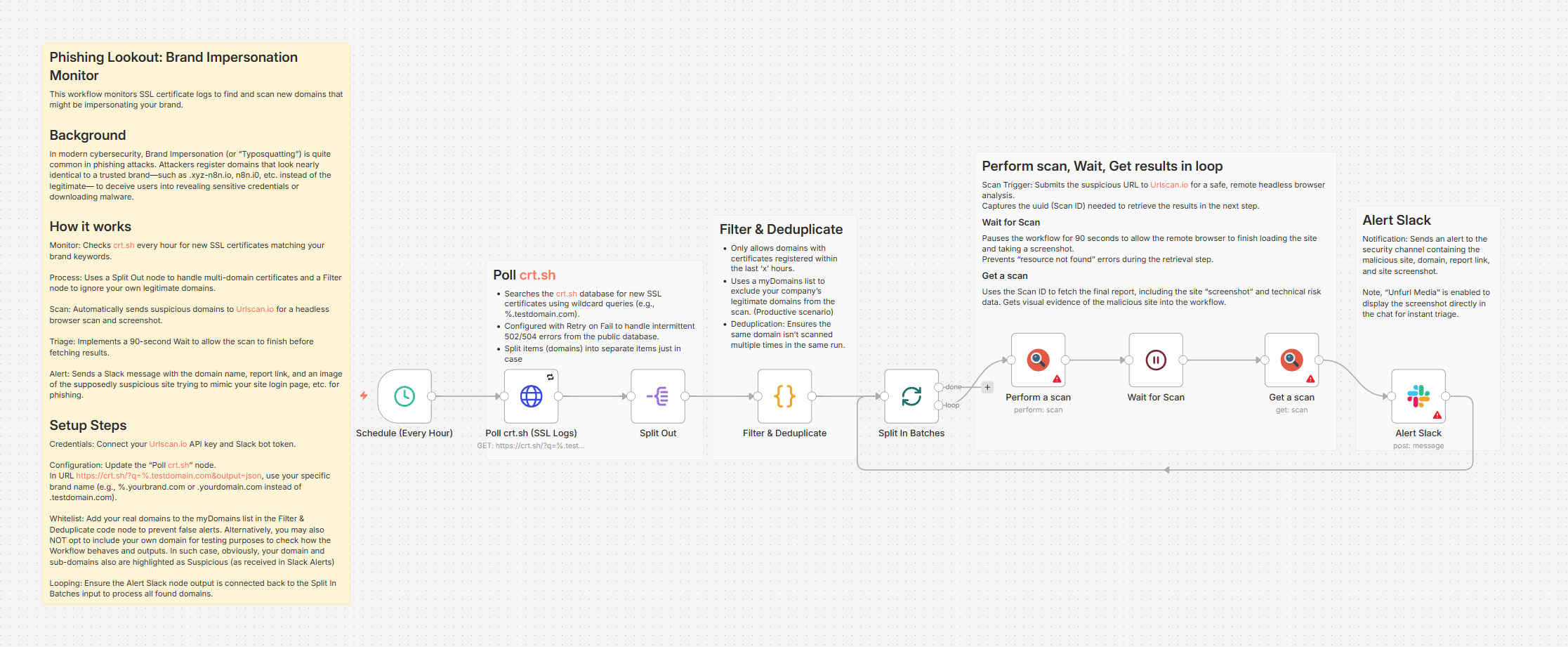
This workflow automates the monitoring of SSL certificates for potential brand-impersonating domains using crt.sh and Urlscan.io. By integrating with Slack, it sends notifications when new suspicious domains are detected. This helps organizations stay vigilant against phishing attacks and typosquatting attempts.
Who Should Use This
This workflow is designed for Security Operations (SecOps) teams, security analysts, and IT professionals responsible for protecting their organization's online reputation and preventing phishing attacks.
Key Features
- Scans SSL certificate logs from crt.sh for new brand-impersonating domains
- Integrates with Urlscan.io to further analyze suspicious domains
- Sends notifications to Slack when new domains are detected
- Provides an early warning system for potential phishing attacks and typosquatting attempts
How to Get Started
To use this workflow, import it into your n8n instance and customize the crt.sh API key, Urlscan.io API key, and Slack channel settings to fit your organization's needs.
Use This Workflow in n8n →Similar Workflows
Affiliate Disclosure: We may earn a commission if you sign up for n8n through our links. This doesn't affect our recommendations.