n8n enterprise AI security firewall — guardrails for secure agents
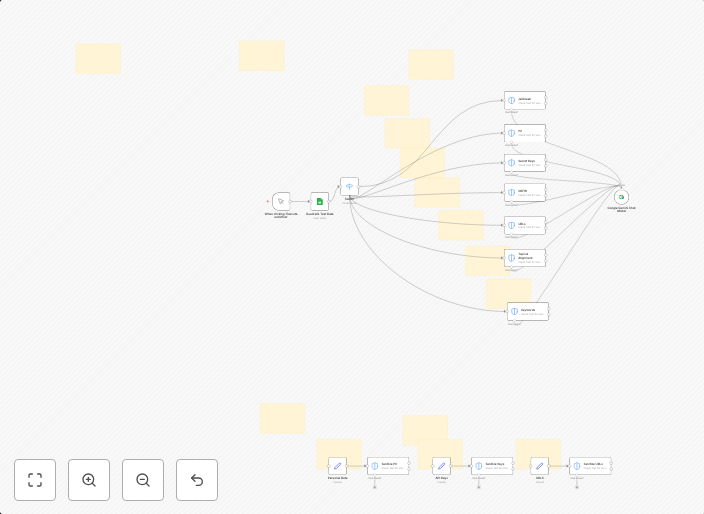
🛡️ n8n Guardrails: Risk Ranking This workflow provides a complete testing rig for evaluating text against seven essential AI guardrails used in production...
Get This WorkflowAbout This Workflow
What This Workflow Does
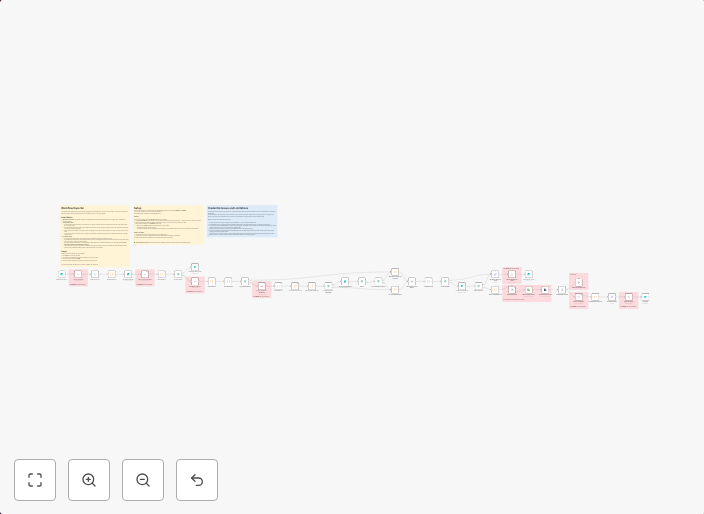
This workflow provides a comprehensive testing rig for evaluating text against seven essential AI guardrails used in production environments. It enables users to assess the risk and security of their AI-powered applications by analyzing text against predefined guardrails. The workflow is designed to help users identify potential security vulnerabilities and ensure compliance with enterprise AI security policies.
Who Should Use This
This workflow is ideal for developers, security professionals, and data analysts working on AI-powered projects who want to ensure the security and integrity of their applications. It is also suitable for businesses and organizations that require robust AI security measures to protect their sensitive data.
Key Features
- Risk Ranking: The workflow evaluates text against seven essential AI guardrails and provides a risk ranking score to help users identify potential security vulnerabilities.
- AI Guardrails: The workflow includes seven essential AI guardrails, including:
- Data protection and confidentiality
- Bias and fairness
- Security and integrity
- Compliance and regulatory requirements
- Transparency and explainability
- Accountability and responsibility
- Intellectual property protection
- Text Analysis: The workflow analyzes text inputs against the AI guardrails to provide a comprehensive evaluation of security risks.
How to Get Started
To use this workflow, simply import it into your n8n instance and customize the workflow settings to fit your specific needs. You can then use the workflow to evaluate text inputs against the AI guardrails and receive a risk ranking score to help you identify potential security vulnerabilities.
Use This Workflow in n8n →Similar Workflows
Affiliate Disclosure: We may earn a commission if you sign up for n8n through our links. This doesn't affect our recommendations.