Validate Seatable webhooks with HMAC SHA256 authentication
📌 Validate Seatable Webhooks with HMAC SHA256 Authentication This mini workflow is designed to securely validate incoming Seatable webhooks using HMAC...
Get This WorkflowAbout This Workflow
Validate Seatable webhooks with HMAC SHA256 authentication
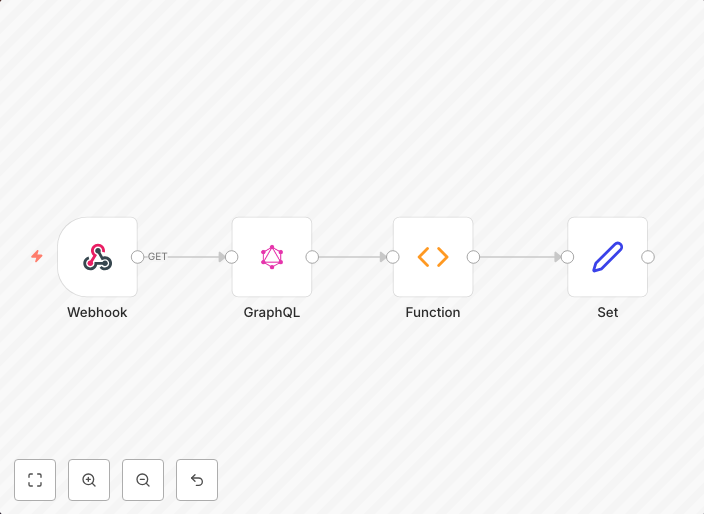
What This Workflow Does
This n8n automation workflow securely validates incoming Seatable webhooks using HMAC SHA256 authentication, ensuring only authorized messages are processed. It verifies the authenticity of webhooks by comparing a provided signature with a calculated one. This prevents malicious actors from sending unauthorized webhooks.
Who Should Use This
Developers and engineers who work with Seatable webhooks and need a reliable solution for authentication and validation should use this workflow. It's particularly useful for companies that rely on webhooks to integrate external services and require robust security measures.
Key Features
- HMAC SHA256 Authentication: The workflow verifies incoming webhooks using a secure HMAC SHA256 algorithm, protecting against unauthorized messages.
- Signature Verification: Calculates and compares a provided signature with a calculated one to ensure webhook authenticity.
- Robust Security: Prevents malicious actors from sending unauthorized webhooks, safeguarding your application's integrity.
- Easy Integration: Seamlessly integrates with existing Seatable webhook infrastructure, minimizing setup and maintenance efforts.
How to Get Started
To use this workflow, import it into your n8n instance and configure the HMAC SHA256 settings according to your Seatable webhook credentials. Customize the workflow as needed to fit your specific application requirements.
Use This Workflow in n8n →Similar Workflows
Affiliate Disclosure: We may earn a commission if you sign up for n8n through our links. This doesn't affect our recommendations.